A activity changer in IT protection
The clock is ticking: although Fortune 500 firms obtain one really serious vulnerability just about every 12 hrs, it will take attackers fewer than 45 minutes to do the exact same as they scan the vastness of the world-wide-web for vulnerable business belongings.
Building matters worse, bad actors are multiplying, very proficient IT pros are a scarce source, and the desire for contactless interactions, remote work preparations, and agile enterprise processes carries on to develop cloud environments. This all puts an organization’s attack surface—the sum whole of the nooks and crannies hackers can pry into—at risk.
“We’ve found a very continuous set of assaults on unique sectors, this kind of as health and fitness treatment, transportation, meals source, and shipping and delivery,” states Gene Spafford, a professor of laptop science at Purdue University. “As just about every of these has transpired, cybersecurity consciousness has risen. Folks really don’t see themselves as victims right until a little something occurs to them—that’s a dilemma. It is not becoming taken critically ample as a prolonged-phrase systemic danger.”
Organizations will have to understand the place the crucial entry details are in their information know-how (IT) environments and how they can reduce their assault area space in a clever, info-driven manner. Electronic belongings aren’t the only merchandise at threat. An organization’s small business status, buyer allegiance, and monetary security all cling in the stability of a company’s cybersecurity posture.
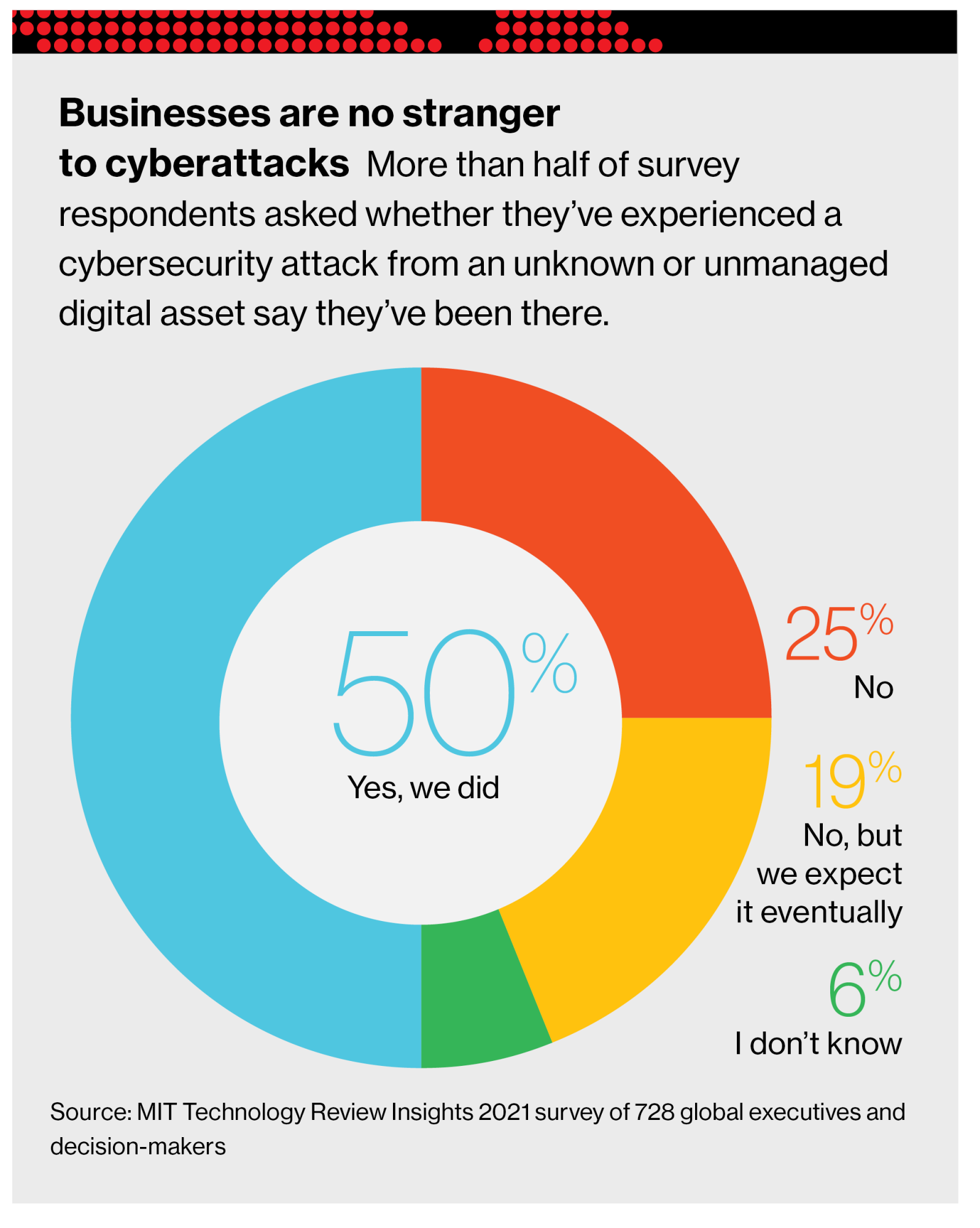
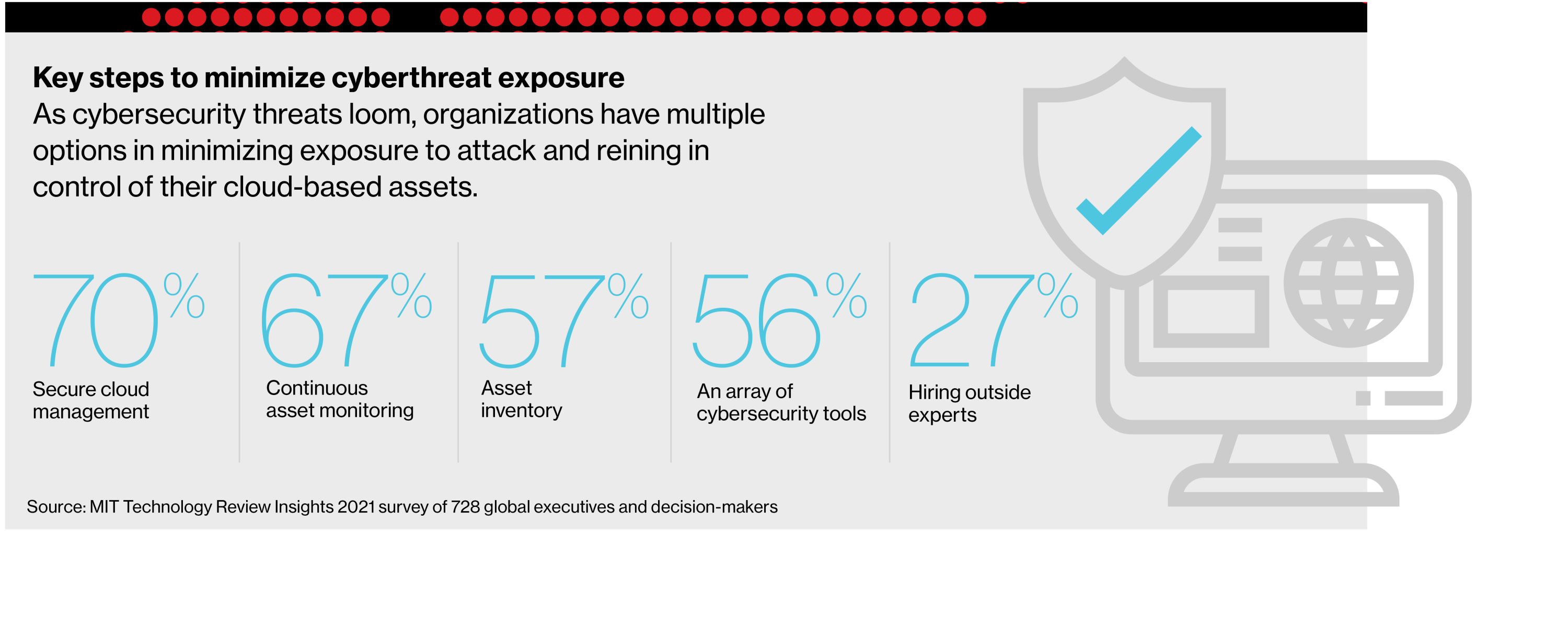
To improved understand the troubles experiencing today’s security teams and the methods they ought to embrace to protect their companies, MIT Technological know-how Assessment Insights and Palo Alto executed a world wide survey of 728 enterprise leaders. Their responses, along with the input of business industry experts, give a critical framework for safeguarding methods in opposition to a rising battalion of terrible actors and quickly-going threats.
The vulnerabilities of a cloud setting
The cloud continues to perform a crucial role in accelerating digital transformation—and for good reason: cloud gives sizeable positive aspects, like increased adaptability, huge expense cost savings, and higher scalability. Nevertheless cloud-centered difficulties comprise 79% of observed exposures in contrast with 21% for on-premises property, according to the “2021 Cortex Xpanse Attack Surface area Threat Report.”
“The cloud is seriously just yet another company’s laptop and storage assets,” suggests Richard Forno, director of the graduate cybersecurity application at the University of Maryland, Baltimore County. “Right there, that offers protection and privateness concerns to providers of all dimensions.”
Even more concerning is this: 49% of study respondents report more than fifty percent of their belongings will be in the general public cloud in 2021. “Ninety-5 % of our business applications are in the cloud, such as CRM, Salesforce, and NetSuite,” suggests Noam Lang, senior director of data safety at Imperva, a cybersecurity software program enterprise, referring to popular subscription-dependent purposes managing shopper marriage management. But though “the cloud offers a great deal additional adaptability and uncomplicated advancement,” Lang adds, “it also makes a large security problem.”
Component of the challenge is the unparalleled pace at which IT teams can spin up cloud servers. “The cadence that we’re functioning at in the cloud can make it significantly a lot more hard, from a stability perspective, to hold monitor of all of the safety upgrades that are necessary,” states Lang.
For case in point, Lang says, in the earlier, deploying on-premises servers entailed time-consuming responsibilities, which includes a lengthy obtaining course of action, deployment things to do, and configuring firewalls. “Just imagine how a great deal time that allowed our stability teams to put together for new servers,” he states. “From the minute we determined to raise our infrastructure, it would take months or months prior to we truly implemented any servers. But in today’s cloud ecosystem, it only normally takes five minutes of shifting code. This will allow us to move the business a lot a lot more rapidly, but it also introduces new risks.”
Download the total report.
This content was manufactured by Insights, the custom written content arm of MIT Technology Review. It was not penned by MIT Technological innovation Review’s editorial personnel.
