
IT safety starts with understanding your assets: Asia-Pacific
A excellent case in point of distant-function stability troubles transpired when an NTUC worker accidentally downloaded malware on to a laptop he was making use of to obtain corporate files by plugging in a personal USB push. “We received a security notify right away, but the remediation was rough,” recalls Loe. “We actually experienced to ship a cybersecurity staffer to the employee’s house on a motorcycle to retrieve the pc for investigation. In the earlier, we could shield the community by just slicing off the employee’s laptop entry. But when an employee is doing the job from household, we cannot take the prospect of getting rid of any knowledge more than the internet.”
Welcome to the new cybersecurity threat landscape, in which 61% of organizations are increasing cybersecurity investment decision in the work-from-house pandemic era, according to a 2021 Gartner CIO Agenda study. Distant employees rely on cloud computing expert services to do their work, no matter whether it is corresponding with co-workers, collaborating on jobs, or signing up for video-conferencing calls with shoppers. And when facts technology (IT) teams, now at a physical clear away, are not responsive to their needs, remote workers can easily shop for their personal on line remedies to troubles. But all that bypasses usual cybersecurity practices—and opens up a entire world of fret for IT.
Nevertheless for several areas of the world, distant operate is just a single of numerous factors expanding an organization’s exposure to cybersecurity breaches. The Asia-Pacific area is no exception, wherever 51% of organizations surveyed by MIT Know-how Overview Insights and Palo Alto Networks report acquiring professional a cybersecurity assault originating from an unknown, unmanaged, or inadequately managed digital asset.
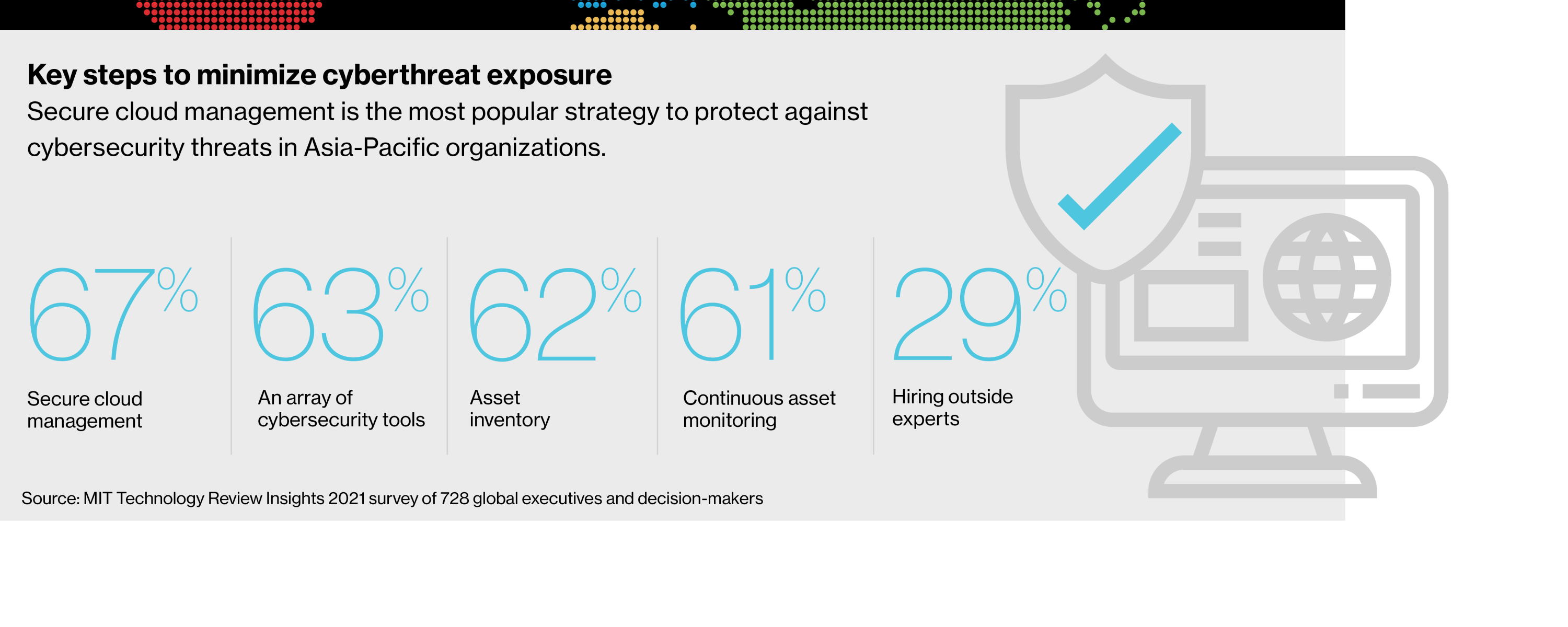
Conducting a comprehensive inventory of web-linked assets and rebooting cybersecurity insurance policies for today’s fashionable remote function setting can mitigate hazards. But organizations must also have an understanding of the cybersecurity tendencies and problems that define their marketplaces, several of which are unique to corporations running in the Asia-Pacific.
To much better comprehend the issues going through today’s stability teams in this region, and the approaches they must embrace, MIT Know-how Evaluate Insights and Palo Alto executed a world wide survey of 728 respondents, 162 from the Asia-Pacific. Their responses, together with the input of industry industry experts, discover unique security problems in today’s IT landscape and supply a crucial framework for safeguarding programs versus a rising battalion of undesirable actors and quick-going threats.
The vulnerabilities of a cloud surroundings
The cloud continues to participate in a important part in accelerating electronic transformation. And for very good reason: cloud systems offer you substantial positive aspects, which include greater versatility, expense discounts, and larger scalability. Yet, cloud environments are responsible for 79% of noticed exposures, in comparison with 21% for on-premises property, according to the 2021 Cortex Xpanse Assault Surface Administration Menace report.
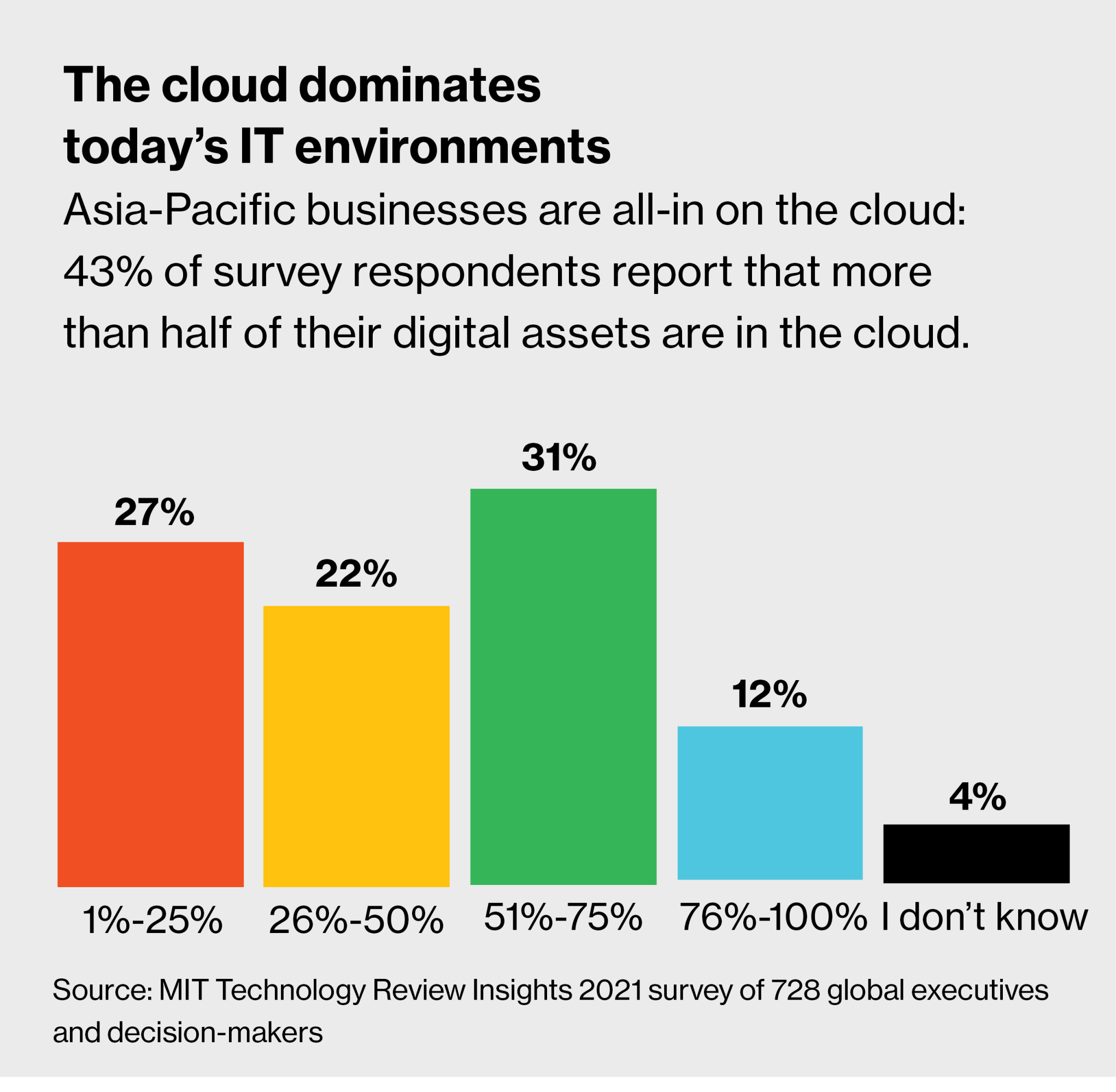
Which is a vital issue, presented that practically fifty percent (43%) of Asia-Pacific organizations report that at least 51% of their functions is in the cloud.
Just one way cloud expert services can compromise an organization’s safety posture is by contributing to shadow IT. Due to the fact cloud computing services can be effortlessly purchased and deployed, Loe states, “procurement electrical power moves from a company’s regular finance place of work to its engineers. With very little much more than a credit rating card, these engineers can acquire a cloud provider without having anyone maintaining keep track of of the buy.” The result, he claims, is “blind spots” that can thwart IT efforts to guard a company’s attack surface— the totality of probable entry points. Just after all, adds Loe, “We cannot guard what we do not know exists—that’s an excessive fact now.”
Biocon’s Agnidipta Sarkar agrees. “Without the paperwork related with procuring IT capabilities, shadow IT can operate rampant,” suggests Sarkar, group main information protection officer (CISO) at the Indian pharmaceutical corporation. “Unless an group actually plans for digital resilience, unplanned and uncontrolled growth of digital belongings can escape the targeted governance that info security requires.”
The exponential growth of interconnected products is also tough organizations to protected their cloud infrastructures. “Many individuals are not knowledgeable that net-of-points units these types of as sensors are really pcs, and that they are effective enough to be applied to start bots and other styles of attacks,” warns Loe. He cites the case in point of intelligent locks and other cellular purposes that allow for workforce to unlock and open doors—and make it possible for hackers to attain unauthorized entry to corporate networks.
Although cloud expert services and interconnected equipment raise universal cybersecurity troubles, Asia-Pacific organizations encounter further worries. For instance, Loe factors to the varying degrees of cybersecurity maturity amid the region’s international locations. “We have nations around the world like Singapore, Japan, and Korea which rank higher in phrases of cyber maturity,” he says. “But we also embody Laos, Cambodia, and Myanmar, which are at the most affordable stop of maturity. In simple fact, some govt officials in these places still use totally free Gmail accounts for formal interaction.” Some susceptible countries have presently been applied as launchpads for assaults on neighbors, Loe suggests.
One more component that distinguished some Asia-Pacific international locations from other areas in the world was an unpreparedness to rapidly pivot to remote function in the early months of the pandemic. In accordance to Kane Lightowler, vice president of Cortex, Palo Alto’s threat detection system division, organizations powering in their electronic transformation attempts “had to prioritize company continuity very first and foremost,” letting cybersecurity to get a again seat. Sadly, he provides, “many of these businesses nonetheless have not caught up to undertaking business enterprise in a safe and compliant manner. Only now, in 2021, are they beginning to prioritize protection again.”
Down load the whole report.
This material was generated by Insights, the customized articles arm of MIT Know-how Evaluation. It was not prepared by MIT Technologies Review’s editorial workers.
