Hackers exploit web-sites to give them fantastic Search engine optimisation prior to deploying malware
Cyberattackers have turned to search motor optimization (Search engine optimisation) strategies to deploy malware payloads to as a lot of victims as doable.
In accordance to Sophos, the so-known as research motor “deoptimization” approach consists of both Seo tips and the abuse of human psychology to press websites that have been compromised up Google’s rankings.
Web optimization optimization is utilized by webmasters to legitimately enhance their website’s publicity on search engines such as Google or Bing. Nonetheless, Sophos suggests that menace actors are now tampering with the information administration units (CMS) of internet sites to serve financial malware, exploit equipment, and ransomware.
In a web site write-up on Monday, the cybersecurity crew mentioned the method, dubbed “Gootloader,” includes deployment of the infection framework for the Gootkit Remote Entry Trojan (RAT) which also provides a variety of other malware payloads.
The use of Web optimization as a strategy to deploy Gootkit RAT is not a small operation. The scientists estimate that a community of servers — 400, if not extra — must be taken care of at any supplied time for good results.
Even though it just isn’t acknowledged if a particular exploit is used to compromise these domains in the first area, the scientists say that CMSs running the backend of internet sites could have been hijacked by way of malware, stolen qualifications, or brute-power assaults.
When the risk actors have received entry, a couple of lines of code are inserted into the system of web page written content. Checks are executed to determine whether the sufferer is of desire as a concentrate on — these kinds of as dependent on their IP and spot — and queries originating from Google research are most commonly acknowledged.
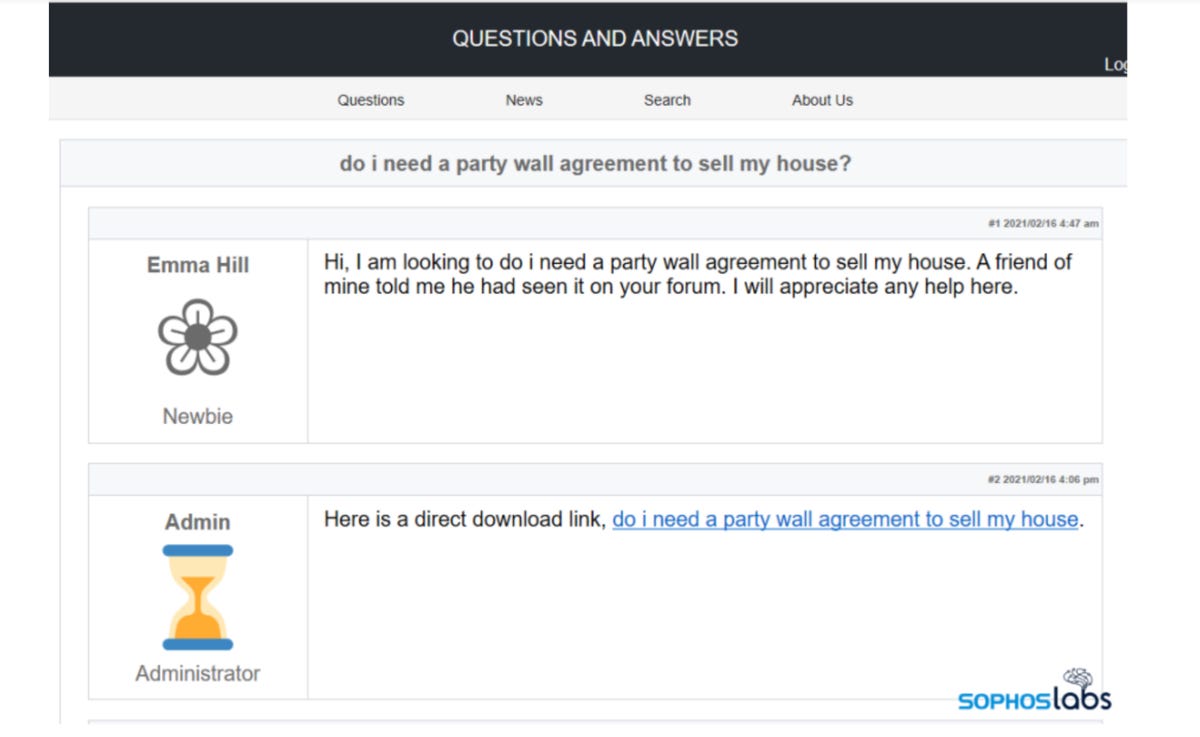
Internet sites compromised by Gootloader are manipulated to solution distinct lookup queries. Pretend message boards are a consistent concept in hacked internet sites observed by Sophos, in which “subtle” modifications are manufactured to “rewrite how the contents of the internet site are introduced to specified people.”
“If the correct conditions are achieved (and there have been no preceding visits to the web site from the visitor’s IP handle), the destructive code jogging server-aspect redraws the web site to give the visitor the visual appearance that they have stumbled into a information board or site reviews space in which people today are discussing exactly the exact same subject matter,” Sophos claims.
If the attackers’ standards usually are not met, the browser will screen a seemingly-regular world wide web site — that ultimately dissolves into garbage text.
A fake discussion board article will then be displayed containing an obvious ‘answer’ to the query, as nicely as a immediate download backlink. In one example talked over by the staff, the internet site of a genuine neonatal clinic was compromised to present ‘answers’ to issues relating to true estate.
Victims who click on the immediate download back links will receive a .zip archive file, named in relation to the research expression, that is made up of a .js file.
The .js file executes, operates in memory, and obfuscated code is then decrypted to connect with other payloads.
According to Sophos, the method is staying applied to distribute the Gootkit banking Trojan, Kronos, Cobalt Strike, and REvil ransomware, amid other malware variants, in South Korea, Germany, France, and the United States.
“At various points, it’s probable for end-users to avoid the infection, if they realize the symptoms,” the scientists say. “The dilemma is that, even educated persons can very easily be fooled by the chain of social engineering methods Gootloader’s creators use. Script blockers like NoScript for Firefox could assistance a careful internet surfer keep on being protected by stopping the original substitute of the hacked net website page to take place, but not everyone works by using these tools.”
Previous and related coverage
Have a idea? Get in touch securely via WhatsApp | Sign at +447713 025 499, or more than at Keybase: charlie0
